
Using Netstumbler To Crack Wep Password
Best practices for wireless network security. First- generation wireless networking placed you between a rock and a hard place.
Should you cave in and deploy a WLAN, despite well- documented protocol vulnerabilities and rampant threats? Or should you try to ban wireless, despite its business advantages and the unnerving suspicion that rogue access points (APs) will crop up anyway? It's no longer a no- win, either/or choice. Recent improvements in wireless protocols and infrastructure technologies make . Donald Welch, associate dean for information and education technology at the U. S. Military Academy at West Point. The academy recently installed a WLAN security suite and plans to offer campus- wide wireless connectivity by fall.
As West Point and thousands of other organizations are now discovering, WLANs can be made secure if you're smart about how you integrate wireless with your wired enterprise, leverage your existing security tools and select the right security technologies- -from basic 8. VPNs to solutions based on the new generation of wireless authentication/encryption protocols. As with any technology, the trick then is to monitor your network's health to keep it safe.
Threats and vulnerabilties. The perils awaiting unprotected WLANs are many. Wireless traffic is easily recorded. Passive eavesdroppers can gather proprietary information, logins, passwords, intranet server addresses, and valid network and station addresses. Intruders can steal Internet bandwidth, transmit spam, or use your network as a springboard to attack others.
WEP Key Converter Have you lost the password to your wireless router? Do you remember the simple codeword that you used the generate that complicated and impossible. Seems like every guide to securing your wireless network tells you to keep your SSID from broadcasting to make your network more secure, but is that really worthwhile?
They can capture and modify traffic to masquerade as you, with financial or legal consequences. Even a low- tech attacker can disrupt your business by launching wireless packet floods against your APs, nearby servers, next- hop wired network or Internet uplink. Fortunately, these risks are not yet heavily exploited. Jupiter Media Research recently reported that 2. WLAN attack in the past year. However, most of these incidents were problems waiting to happen: rogue APs, stations associating with the wrong AP and war driving.
Serious security breaches- -like wired network intrusion, theft of confidential data and forgery- -were far less common, according to the survey. In short, early adopters have been lucky. The cost of downtime and cleanup can be an order of magnitude greater than the cost of prevention. Now is the time to start playing catch- up with WLAN security. Steps to securing wireless networks. If you don't know what you're defending and why, your security measures are just shots in the dark.
It's critical to identify business assets that must be protected and the impact of damage, theft or loss. For wireless network security, as with dial- up and DSL, your policy management should define access requirements. Math Resource Studio 4 Keygen Crack more. Who needs access to what and when? If your company already has a remote access policy for travelers and telecommuters, expand it to incorporate wireless.
If you have no such policy, create one. Remember to include scenarios that are unique to wireless, like employees at public hot spots (see . Few companies offer Ethernet access to visiting customers or business partners. Jacks in public areas are typically disabled or latched to known addresses. But wireless laptops and mobile devices can easily associate with nearby APs or other wireless stations. This is both a threat and an opportunity. Security policies should define rules for .
For example, you may prohibit peer- to- peer networking while permitting logged guest sessions through specific APs with limited destinations, protocols, duration and bandwidth. If guest access is banned, your policy must state this so that steps can be taken to prevent visitor intrusion. Once assets have been identified, enumerate threats and quantify risks. Security is always a balancing act, weighing risk against cost.
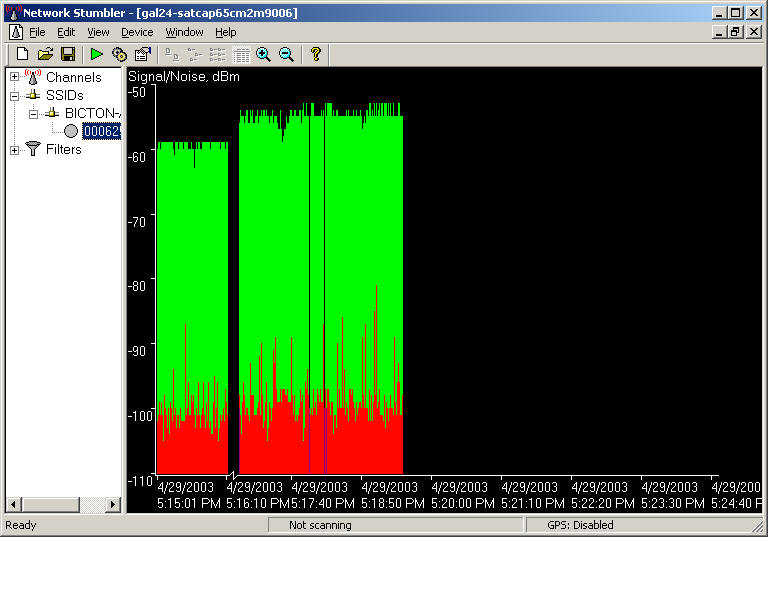
After this foundation has been established, you can begin to consider WLAN implementation alternatives. Taking stock. Before you plot out access point deployment, conduct a site survey using a WLAN discovery tool such as Net. Stumbler. What you learn might surprise you. According to a recent Gartner report, at least one in five companies find APs deployed without IT department permission. Commodity pricing, retail distribution and setup wizards have made it trivial for employees to install rogue APs, which can expose corporate assets to outsiders and interfere with WLAN performance. Find and eliminate rogue APs from the start- -or safely incorporate them into your wireless network design.
Site surveys also turn up unauthorized workstations. Create an inventory of laptops and mobile devices with wireless adapters, documenting user, MAC address and operating system. This will be used to implement WLAN access controls. And you'll find an up- to- date list is essential when WLAN adapters are lost or stolen. You may find nearby APs and stations that don't belong to you. Survey public areas (parking lots, hallways, lobbies) just beyond the physical boundaries of your facility, including upstairs and downstairs.
Neighboring MAC addresses should be recorded, along with network name (SSID) and channel. This list will be used to avoid cross- channel interference and eliminate false- positive intrusion alerts. Consider getting APs with high- grade antennas that produce strong yet tight signals.
These provide focused connectivity for your users. At the same time, their narrow focus means the signals are less likely to spill out into the street, where a war driver can capture and exploit it.
Aircrack is a suite of tools for 802.11a/b/g WEP and WPA cracking. It implements the best known cracking algorithms to recover wireless keys once enough encrypted. Telecommuting is pretty easy now. Skype, Slack, and good ol’ Gchat—excuse me, Google Hangouts—make communicating with your colleagues down the hall or around. Internet has become one of the most important requirement of today’s life. In fact, for some of us, it is the source of income. With the increasing use of. Website dedicated to Wireless LAN Security and Wardriving. Includes lots of whitepapers, presentations, tools, firmware, drivers, equipment, and resources.
WLAN meets LANConsider how new WLAN segments will be integrated with and reuse components of your wired infrastructure. Your network topology, device placement and current security measures all have direct impact on wireless LAN security. Restrict AP placement in your network topology. Wireless applications require protected access to the intranet and/or Internet, affecting routers, firewall rules and VPN policies. Wireless APs are untrusted entities and should always sit outside the firewall or within a DMZ- -never inside the firewall.
Think in terms of a three- interface firewall- -intranet on the inside, APs (and other public servers) on the DMZ, and Internet on the outside interface. Circumstances dictate whether your APs should sit on the DMZ or outside. A DMZ can protect the WLAN from Internet threats while protecting the wired intranet from WLAN threats. However, for example, if your firewall doesn't let VPN tunnels originate in the DMZ, you may need to place your AP on the outside interface instead. AP security capabilities vary greatly. Entry- level APs are essentially .
Enterprise- grade APs, such as Cisco Systems' Aironet 1. Proxim's ORi. NOCO AP- 2. X port access control (more on this a bit later).
If existing firewalls have spare capacity, they may be leveraged to secure your new WLAN. However, WLANs require more bandwidth per user than v. Smart APs can offload VPN processing, placing fewer demands on the firewall. Another option is to concentrate access at a new type device: a gateway tailored for wireless LANs. Wireless stations usually have DHCP addresses, so packet inspection needs to occur at both MAC address and user levels.
WLAN gateways, such as those from Bluesocket, Vernier and Reef. Edge, enforce scalable policies based on groups of users/stations rather than source IP. They may also provide SSL portals for visitor login or VPN tunnel persistence when stations roam from one AP to another. Specialized WLAN gateways complement, but don't replace, general- purpose Internet firewalls. After entering the wired network, wireless traffic should be segregated so that different policies can be applied.
Intranet servers, edge routers and bandwidth managers can be updated to filter on subnet(s) assigned to your WLAN. Even when addresses are hidden behind Network Address Translation (NAT), Virtual LAN (VLAN) tags can be used to avoid broadcasting wireless traffic throughout your Intranet. Leverage existing security.